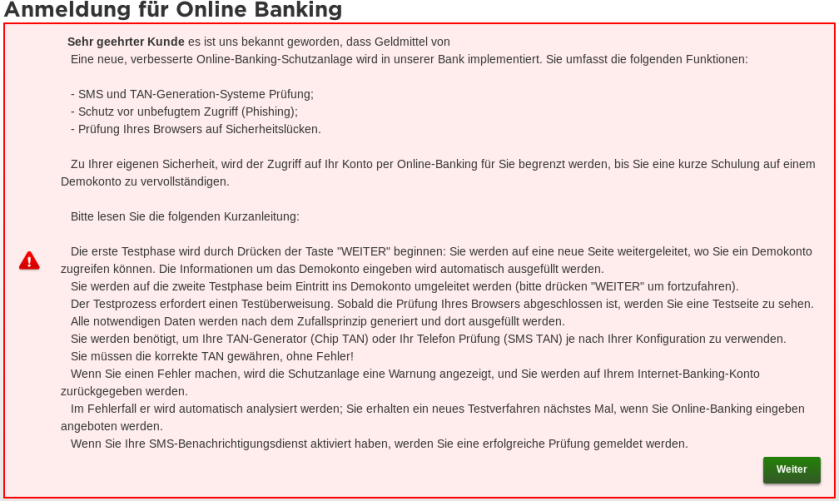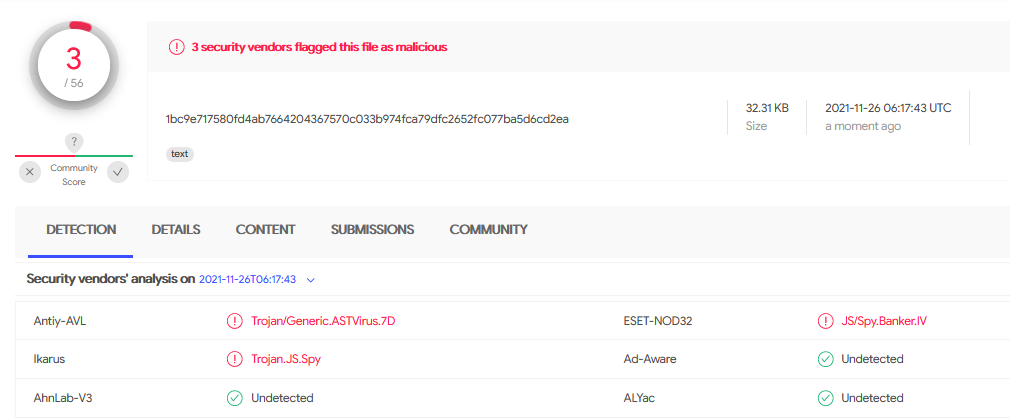
PDF) Review of Browser Extensions, a Man-in-the-Browser Phishing Techniques Targeting Bank Customers

PDF) Intraoperative laser angiography using the SPY system: Review of the literature and recommendations for use
PDF) Intraoperative laser angiography using the SPY system: Review of the literature and recommendations for use

PDF) Intraoperative laser angiography using the SPY system: Review of the literature and recommendations for use

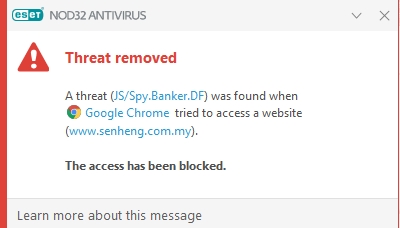
HTML/ScrInject.B koń trojański - Malware on web - Malware Finding and Cleaning - ESET Security Forum

Exercise under heat stress: thermoregulation, hydration, performance implications, and mitigation strategies | Physiological Reviews

PDF) Intraoperative laser angiography using the SPY system: Review of the literature and recommendations for use